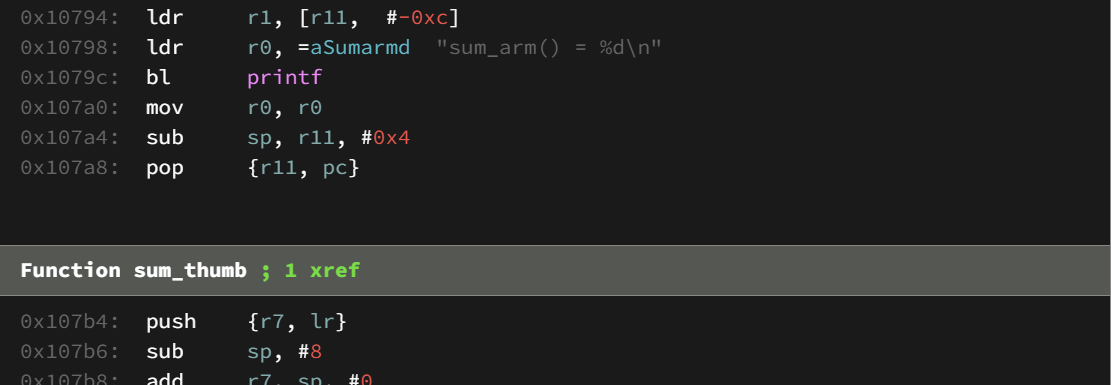
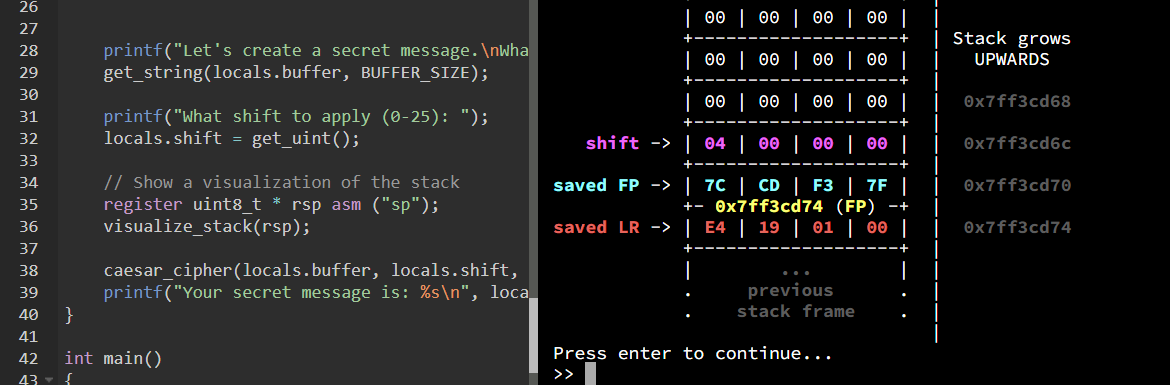
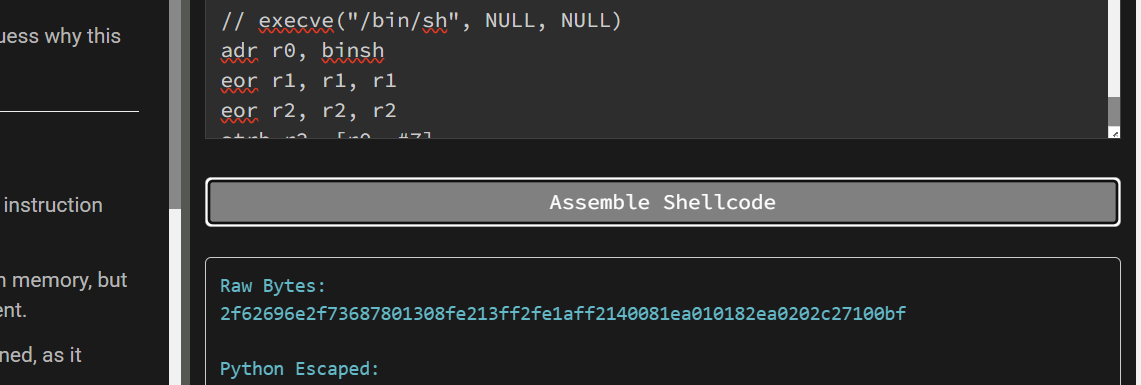
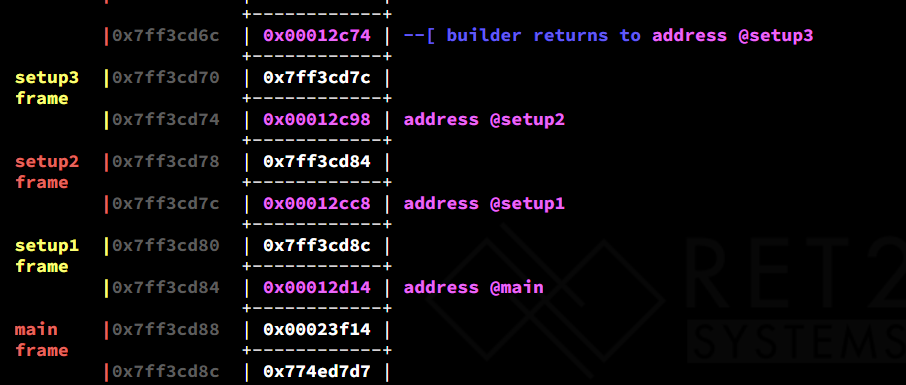
Before diving headfirst into exploitation, it is important to be comfortable reading, navigating, and understanding ARM assembly code.
This chapter will highlight major differences between x86-64 and ARM architectures while providing a series of increasingly difficult challenges that highlight those differences.- Introduction to ARM & Thumb Assembly concepts
- Calling Conventions on ARM
- ARM Addressing Modes & Conditional Suffixes